$1,500,000,000 Cartel Network Exposed in Minneapolis — 3.25 Tons Seized, 2 Judges Arrested.lh

4:17 a.m.
Minneapolis early morning.
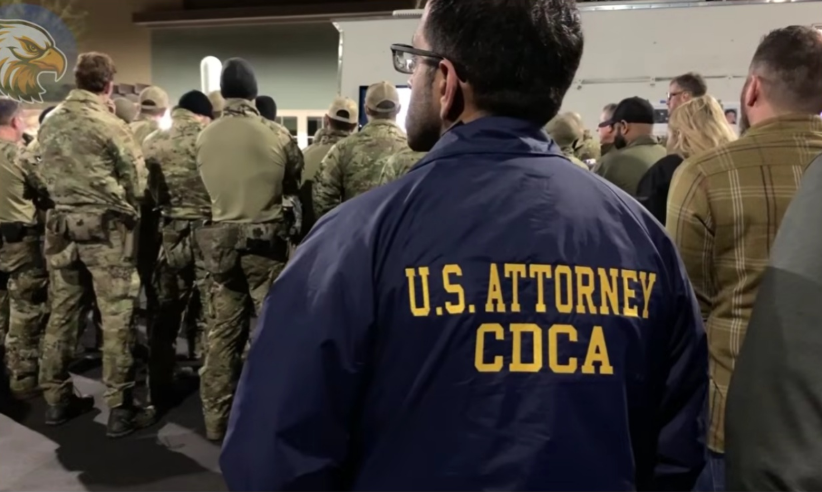
In a single pre-dawn operation, federal agencies revealed numbers that immediately stunned the country.
Investigators confirmed that 3.25 25 tons of cocaine had been seized along with more than $6.
9 million potentially lethal doses of fentinel while $1.
5 billion in illicit money was traced through what appeared to be legitimate financial networks.
Two sitting judges were taken into custody at their private residences and more than 1,000 federal agents were deployed within just a few hours.
These figures did not come from rumors or online speculation.
They appeared in breaking news alerts, in FBI press briefings, and on evidence tables covered with cash, narcotics, and encrypted devices sealed only hours earlier.
Everything pointed to a case far larger and far more dangerous than a routine drug bust.
As Minneapolis remained quiet under early morning fog, while most residents were still asleep, federal strike teams moved into position with precise timing.
There were no sirens and no public warnings.
Only coordinated breaches, secured servers, and suspects detained before any data could be erased or any calls could be made.
This was not a rushed raid, but a carefully planned operation designed to collapse an entire network in silence.
What made this operation truly alarming was not just the scale of drugs and money involved, but the status of those arrested.

These were not street level traffickers or shadowy couriers.
They were judges, people trusted to sign warrants, oversee prosecutions, and decide the outcome of drug and financial crime cases for years.
This was not simply a drug case.
It was a direct strike against the American justice system itself.
What federal agents uncovered suggests that cartel power does not always rely on violence or intimidation, but on access, influence, and decisions made quietly inside institutions meant to protect the public.
If you want to understand how this network was built, who stood at the center of it, and why it took years for federal authorities to move, subscribe to military power now.
Because what comes next reveals how deep this infiltration truly went.
Long before federal teams moved into position, Minneapolis and the broader Midwest had already become a quiet focal point for federal investigators.
The region sits at the intersection of major interstate highways, rail lines, and distribution hubs that connect the East Coast, the Great Lakes, and the Central United States.
Warehouses, trucking companies, and logistics firms operate around the clock, moving legitimate goods across state lines every day.
On the surface, it looks like economic efficiency.
Beneath it, the same infrastructure creates ideal conditions for illicit traffic to blend in and move unnoticed.
Over several years, law enforcement agencies tracked a steady rise in serious drug cases involving fentinyl, cocaine, and other synthetic narcotics.
Arrests were frequent, seizures were announced, and task forces were expanded.
Yet, despite the growing volume of cases, the outcomes often failed to match expectations.
High-risk suspects were released earlier than anticipated.
Charges were quietly reduced.
Evidence that once appeared solid was suddenly ruled insufficient.
In isolation, each decision followed legal procedure.
Taken together, the pattern became difficult to ignore.
FBI and ICE analysts began reviewing these cases side by side rather than individually.
When they did, similarities emerged that could not be explained by coincidence.
Certain types of defendants consistently avoided long-term detention.
Search warrants stalled at key moments.
Large sums of seized cash were returned through narrowly framed legal arguments that surfaced repeatedly, even when the cases themselves had little in common.
What initially looked like administrative delay began to resemble something more deliberate.
The first true red flag came from a routine audit of digital court records.
Analysts noticed that a series of electronic files had been altered after official submission.
The changes were subtle and technically legal, but each modification carried the same digital approval signature.
Different judges, different cases, different timelines.
Yet, the authorization appeared at precisely the moment when outcomes shifted.
It was not obvious enough to trigger alarms on its own, but consistent enough to raise quiet concern.
At that stage, investigators stopped treating the situation as a procedural problem.
The evidence suggested the system was not malfunctioning.
It was responding exactly as someone intended.
What they were looking at was not failure, but control, exercised from within the very framework designed to enforce the law.
Just before dawn, more than 200 federal agents began moving at the same time.
FBI, ICE, DEA, and local tactical units advanced according to a synchronized plan that left no room for delay or improvisation.
Vehicles without markings rolled into position.
Teams exited quietly.
Timelines were checked one final time.
Every movement had been rehearsed because speed mattered more than force.
The first priority was clear.
Target one was a luxury high-rise condominium located in one of the city’s most desirable districts.
The residents belong to two sitting judges, individuals entrusted with overseeing criminal cases, approving warrants, and making sentencing decisions that shaped the outcome of drug and financial prosecutions across the region.
To federal planners, this location carried more risk than any stash house or warehouse.
If anything went wrong here, evidence could disappear in seconds.
At the exact moment the signal was given, the entry team moved.
The door was breached in a single controlled action designed to overwhelm before confusion could turn into resistance.
Agents flowed into the apartment with practiced precision, securing rooms and occupants before anyone inside could reach a phone, a laptop, or a network connection.
Electronic devices were seized immediately.
Laptops were closed midsession.
Phones were taken from charging cables.
External drives were disconnected and placed into shielded containers.
Every second counted because investigators understood that the most valuable evidence in this case was not physical.
It lived in data, timestamps, and encrypted files that could be wiped clean with a single command.
As the residence was secured, agents began their initial sweep.
What they found confirmed that this was no ordinary home search.
Large amounts of cash were recovered, packaged carefully, and stored away from everyday living spaces.
Bricks of cocaine were discovered hidden behind false panels, not in quantities associated with personal use or casual trafficking, but in amounts that suggested coordination and confidence.
Encrypted hard drives were located in secure compartments, clearly separated from regular household electronics.
These discoveries were logged quickly, photographed, and removed for processing.
The goal was not to catalog everything on site.
It was to secure the critical pieces and move on.
The operation was designed to unfold across the city, not linger in a single location.
While target one was being secured, similar scenes were playing out elsewhere.
Across Minneapolis and into surrounding areas, federal teams were executing warrants at more than 17 locations simultaneously.
Apartments, offices, storage facilities, and business fronts were all hit within the same narrow window.
No single target was allowed to warn another.
No communication was permitted to escape the perimeter.
From the command perspective, this was the most fragile phase of the entire operation.
If even one location failed to hold, if one suspect managed to send a message or trigger a data wipe, months of preparation could collapse in minutes.
That risk was precisely why everything was happening at once.
As reports came in, one detail became immediately clear.
The operation was working.
Devices were being secured intact.
Suspects were in custody.
Evidence was being preserved before it could vanish.
As the first wave of arrests unfolded, federal teams moved immediately to a second layer of targets.
These locations did not look like crime scenes.
They looked legitimate, clean, and ordinary.
The kind of places people passed every day without a second thought.
Law offices with glass doors and professional signage.
Logistics companies operating out of modern industrial parks.
Warehouses sitting quietly on the outskirts of the city, surrounded by loading docks and security cameras.
At the first location, a registered legal office, agents expected case files, client records, and court correspondence.
Instead, they found empty desks, unused conference rooms, and filing cabinets filled with carefully arranged but meaningless paperwork.
There were no active clients, no ongoing cases, and no real legal work being performed.
What appeared to be a functioning law firm existed only on paper.
Electronic equipment told a different story.
Server racks were running continuously.
Hard drives were labeled with internal codes rather than case names.
Digital ledgers tracked transfers moving in and out of accounts that did not belong to any identifiable clients.
The space was not designed to practice law.
The space was not designed to practice law.
It was designed to move money quietly while looking legitimate.
At nearby logistics companies, the pattern repeated itself.
On the surface, everything checked out.
Shipping manifests were in order, vehicles were registered, employees showed up on payroll records, but when agents followed the data, the transactions led nowhere meaningful.
Goods were listed as transferred, but delivery confirmations were vague or missing.
Inventory records did not match physical stock.
Payments flowed through multiple layers of subcontractors that existed only as shell entities.
In suburban warehouse districts, teams breached facilities that appeared clean and well organized.
Pallets were stacked neatly.
Forklifts were parked in assigned areas.
Safety signage hung on the walls.
Yet behind this appearance of order, there were no real customers and no commercial activity consistent with the volume being reported.
What these locations handled was not product, but movement.
The kind that leaves as little trace as possible.
Investigators quickly realized they were not looking at traditional drug fronts.
There were no obvious stash houses and no visible street level operations.
Instead, the cartel had embedded itself inside legal and logistical infrastructure that already moved massive volumes of goods every day.
By doing so, illegal shipments blended into normal commerce, passing inspections and audits simply by not standing out.
This approach offered several advantages.
Traditional trafficking routes rely on speed, secrecy, and risk.











